Local DNS and IOS16
After upgrading to IOS16 on several devices we recognized an issue according to name resolution. Our DHCP-Server offered two types of DNS entries to clients: Some local DNS servers and two Cloudflare ones. This worked like a charm for years. After upgrading our IOS devices we recognized after a while that all local addresses are no longer resolved to addresses. Each time we tried to connect to an office server by name the name could not be resolved.
After some testing with several other devices (macOS, Windows, Linux) we were completely lost: All devices were able to use the DNS system and connect to any server in the office - except the ios ones.
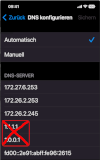
Checking the configuration of our ios devices showed up all necessary DNS servers and the configured fallback to Cloudflare servers. The only difference between the local and the Cloudflare servers is the ability to use DNS over HTTPS. Cloudflare is able, but our local servers are not. To quickly solve this issue we tried to deactivate the Cloudflare servers on our ios-devices - and the DNS system worked as expected.
In the next step, we changed the DNS distribution of our DHCP servers to drop all external DNS servers, which solved the problem immediately.
Enabling DNS over HTTPS on local DNS servers would be a different solution to overcome this issue.